Democratic Censorship Unplugs Zip-gun
More on Dvorak, Democratization of Censorship, 3D Printed Gun plans take down, Google Open-sources an amazing image detection tool, Miles and Lyle argue about the ability for computers to program, social security and laws, virtual machines for browsers and malware detection and much more Geek News of the week.
Feedback from Last Week "We-Vibe's Update increases Battery Range to reach New York"
VI, Emacs, and Cursor Movement
Our informal poll told us that half of you like Vi and the other half like Emacs. And that half of the Emacs users can get by in Vi.
From listener Marcus:
BTW, the hjkl keyboard movement is loosly based on the ASCII meanings for control characters, ^H is backspace, ^J is linefeed. The old ADM3A terminal used ^H, ^J, ^K, ^L for the cursor movement (I think that they were the first to use this near “standard”). This was before the VT100 and ANSI escape sequences for cursor movement. Remember that the ADM3A was implemented in a single board of 7400 series ICs, so dealing with multi character escape sequences was a lot harder than single control character actions.
From listener Janine:
I live and work in the East Bay, and vim has been my editor of choice for pretty much my entire career as a software engineer. It’s efficient and works for everything I need, so why switch?
Dvorak
From Listener Steve (SRF)
Dvorak layout was pushed, decades ago, as being x% (or even xX, if you see what I mean) faster than Qwerty, but that was something between marketing hype and pure lie. I think testing shows that experienced Dvorak typists average 5-10% faster than experienced Qwerty typists. Hardly worth the effort of switching.
[Where] Dvorak shines is in reduced wrist strain. I switched 17 years ago or thereabouts. My wrists were getting torn up by 80 hours a week of programming and writing. Ergo keyboards helped some. Dvorak helped more. Now I mostly use Dvorak on a Kinesis ergo keyboard, and wrist and hand soreness is a thing of the past. (The Kinesis Classic keyboard, by the way, is a thing of beauty. It takes some getting used to, but after that it’s a “cold, dead hands” peripheral.)
Court: With 3D printer gun files, national security interest trumps free speech | Ars Technica
A federal appeals court ruled Tuesday against Defense Distributed, the Texas organization that promotes 3D-printed guns, in a lawsuit that it brought last year against the State Department.
In a 2-1 decision, the 5th Circuit Court of Appeals was not persuaded that Defense Distributed
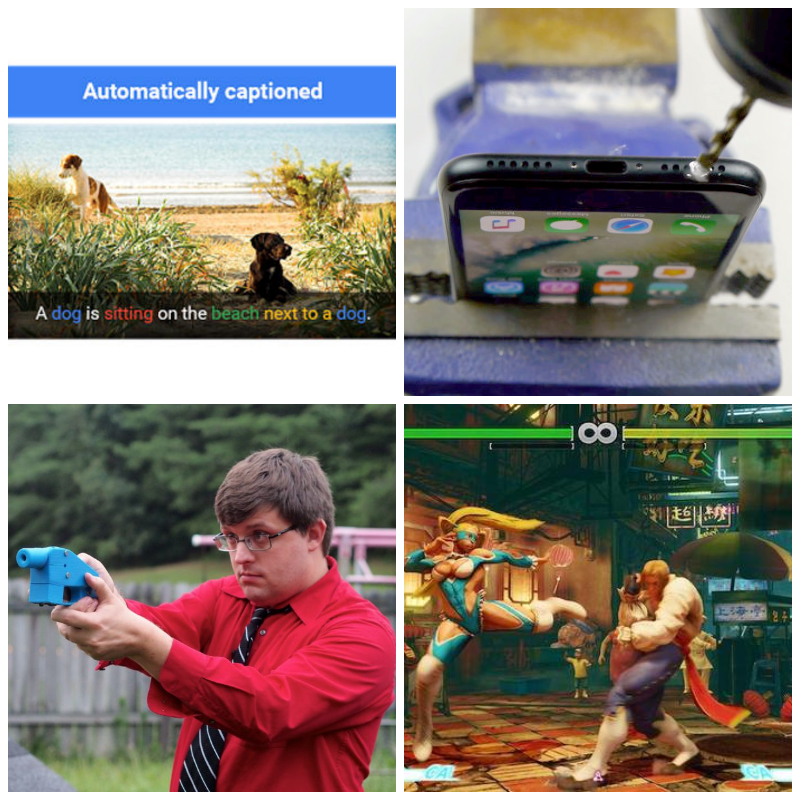
What's in that photo? Google open-sources caption tool in TensorFlow that can tell you
Google has open-sourced a model for its machine-learning system, called Show and Tell, which can view an image and generate accurate and original captions.
As we speak, teen social site is leaking millions of plaintext passwords
A social hangout website for teenage girls has sprung a leak that’s exposing plaintext passwords protecting as many as 5.5 million user accounts. As this post went live, all attempts to get the leak plugged had failed.
California Enacts Law Requiring IMDb to Remove Actor Ages on Request
California Gov. Jerry Brown on Saturday signed legislation that requires certain entertainment sites, such as IMDb, to remove
Windows 10 will soon run Edge in a virtual machine to keep you safe
Microsoft has announced that the next major update to Windows 10 will run its Edge browser in a lightweight virtual machine. Running the update in a virtual machine will make exploiting the browser and attacking the operating system or compromising user data more challenging.
How climate science deniers can accept so many 'impossible things' all at once
Occasionally, contrarians will say that no single weather event can prove human-caused global warming. But then they
Double KO! Capcom's Street Fighter V installs hidden rootkit on PCs
A fresh update for Capcom’s Street Fighter V for PCs includes a knock-out move: a secret rootkit that gives any installed application kernel-level privileges.
People Are Actually Drilling Holes Into Their iPhone 7 to "Make a Headphone Jack"
Last week YouTuber
Reddit brings down North Korea's entire internet after links to country's 28 websites are posted online
All 28 websites on North Korea’s version of the internet were opened to outsiders, causing a surge of demand that flooded the state’s systems
Malware Evades Detection with Novel Technique
The malware, according to researcher Caleb Fenton with security firm SentinelOne, evades detection simply by counting the number of documents
e40 s16

