Warrant-less Flashing Kills Drone’s Battery
California has a new privacy law, Flash has a huge problem, and Siri can be hacked. Also Facebook’s iOS app sucks battery life, quantum gravity experiment is possible, Apple vs University of Wisconsin-Madison and some more geeky weekly news.
Adobe Flash Player Security Vulnerability: How to protect yourself
Just one day after Adobe released its monthly security patches for various software including Flash Player, the company confirmed a major security vulnerability that affects all versions of Flash for Windows, Mac and Linux computers. You read that correctly
How to Enable Click-to-Play Plugins in Every Web Browser
Most web browsers load Flash and other plug-in content as soon as you open a web page. Enable
ClickToPlugin & ClickToFlash Safari extensions
For Safari “ClickToPlugin is a lightweight and highly customizable extension that prevents Safari from launching plug-ins automatically”
Flashblock :: Add-ons for Firefox
For Firefox “Never be annoyed by a Flash animation again! Blocks Flash so it won’t get in your way, but if you want to see it, just click on…”
Flashcontrol - Chrome Web Store
For Chrome “Prevents Flash content from loading unless you allow it.”
Gov. Brown Signs CalECPA
After months of pressure from public interest groups, media organizations, privacy advocates, tech companies, and thousands of members of the public, California
Facebook now notifies you if you’re the target of a state-sponsored attack
Facebook is now issuing warning messages to users if it strongly suspects that an account is being targeted by a hacker working for a nation state. The message (pictured above) also recommends that users turn on “Login Approvals,” which means accounts can only be accessed using stronger two-factor authentication.
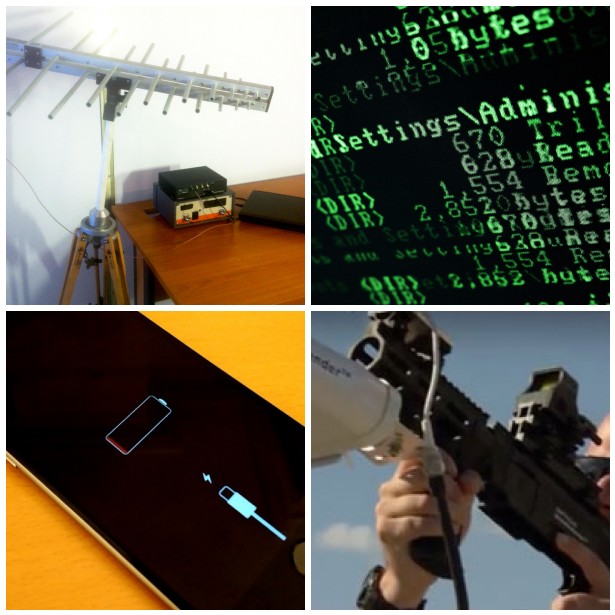
Point-and-shoot weapon stops drones without destroying them
This can be achieved with DroneDefender, a recently made available “gun” that uses radio control frequency disruption technologies to safely stop drones in the air, before they can pose a threat to military or civilian safety.
The tool is a point-and-shoot system, and has a range of some 400 meters. It gains control of the drone, immobilizing it so no remote action can occur. It does so by either disrupting remote control or GPS navigation.
The drone then either lands in the vicinity or flies back to its starting point, and effectively suffers no damage.
Hackers Use Head phones and Voice Commands to control phones
A pair of researchers at ANSSI, a French government agency devoted to information security, have shown that they can use radio waves to silently trigger voice commands on any Android phone or iPhone that has Google Now or Siri enabled, if it also has a pair of headphones with a microphone plugged into its jack. Their clever hack uses those headphones
A New Experiment May Determine Whether Gravity Is Quantized
Experimentalists are bringing increasingly massive systems into quantum states. They are now close to masses where they might be able to just measure what happens to the gravitational field.
Apple Loses Patent Battle with University
Apple Inc could be facing up to $862 million in damages after a U.S. jury on Tuesday found the iPhone maker used technology owned by the University of Wisconsin-Madison’s licensing arm without permission in chips found in many of its most popular devices.
The jury in Madison, Wisconsin also said the patent, which improves processor efficiency, was valid. The trial will now move on to determine how much Apple owes in damages.

